Welcome to the fourth part of this series on “Reverse Engineering android applications”. To read an overview of the series, refer to the serious announcement blog post.
So far all the parts in this series are on offline tools for Reverse engineering, in this part we will cover popular online android analysis tools, that help us to perform reverse engineering on apk and help us determine whether app is malicious or not.
Online tools provide reports based on sandbox testing, these reports can be research base for analyzing any application before reversing source code in any offline tool.
For instance, if online report shows that application is using Socket connection in particular Class file, then we need to focus on reversing that class file only, rather than examining a whole set of classes.
We will see about this set of tools:
- Anubis
- Mobile-Sandbox
- Sanddroid
- Dexter
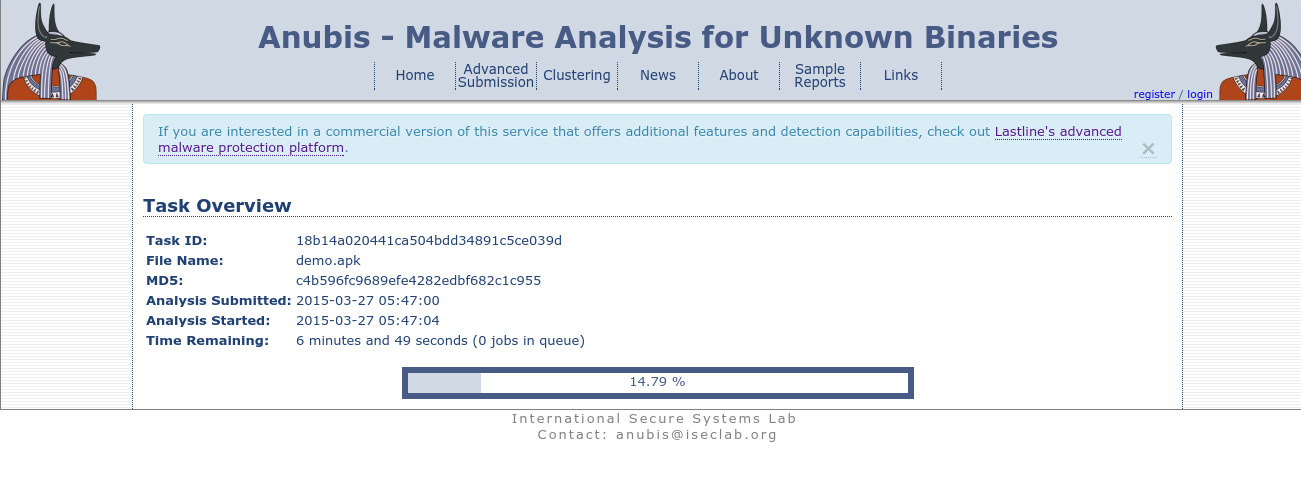
Anubis
Anubis is one of the oldest online web service, which executes android and windows binaries inside its sandbox environment, providing detailed report of dynamic analysis as well as static analysis.
All we need to do is submit an apk file for analysis on Anubis. After submitting, it will take time to execute and generate reports depending on your application.
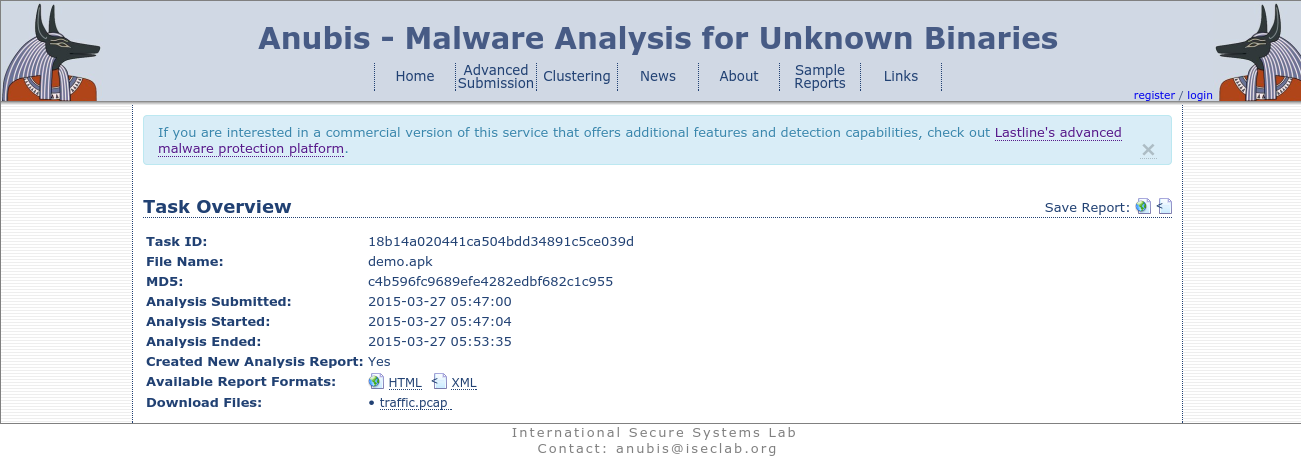
It will generate report after successful completion, also if malicious app contains network connection, then report will generate .pcap file, which can be opened in wireshark to analyzed.
Here is a sample report provided by Anubis after examining a malicious application.
Mobile-Sandbox
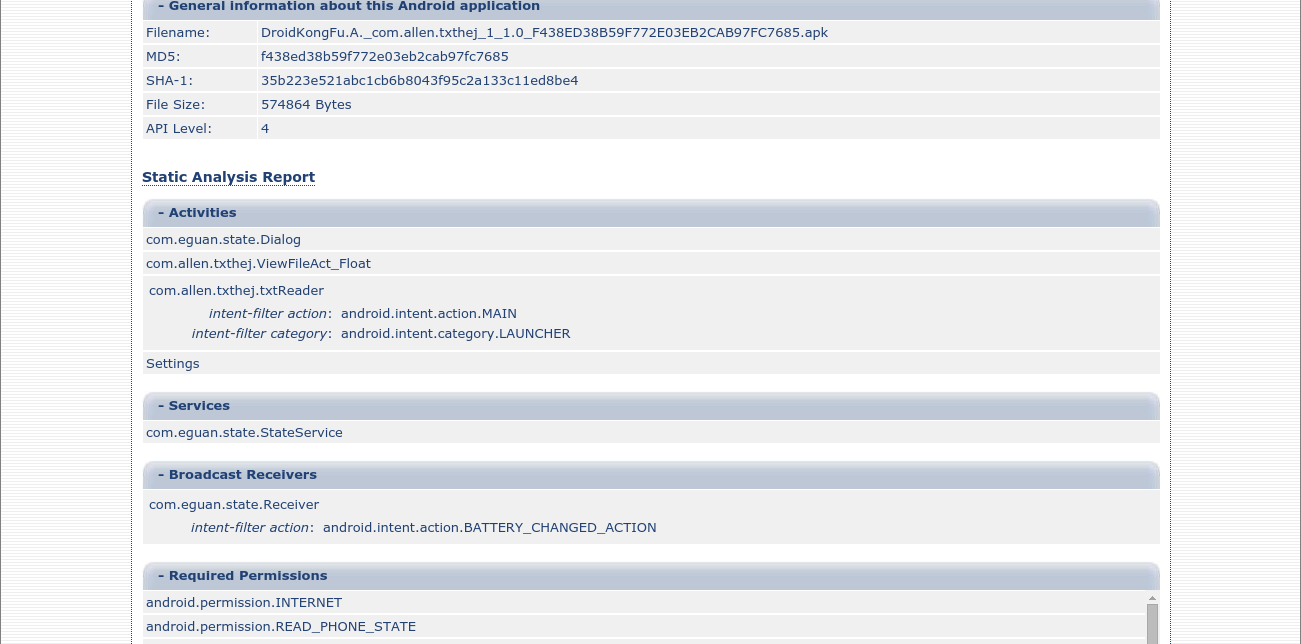
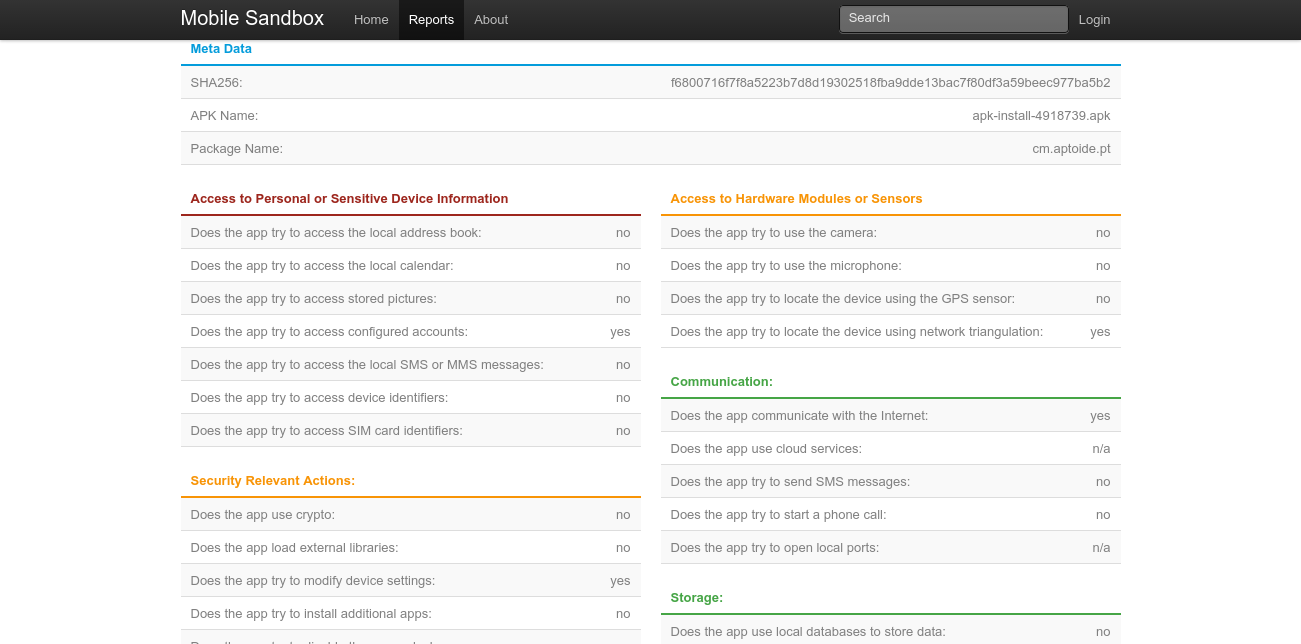
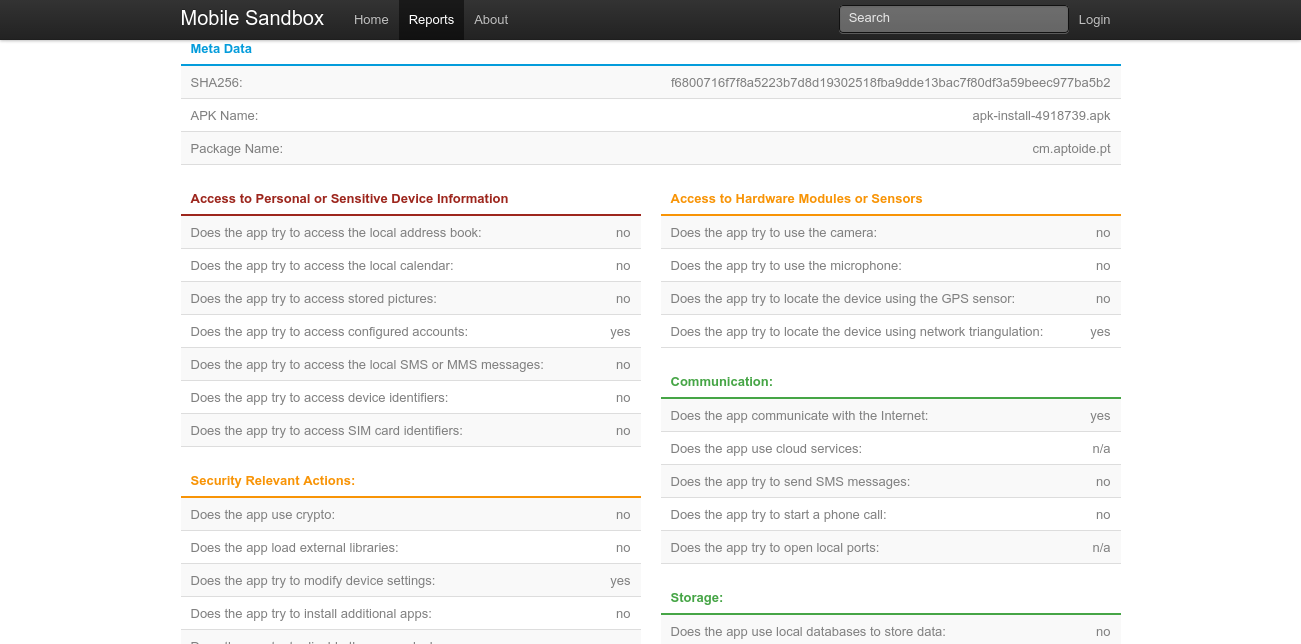
Same as Anubis, Mobile-Sandbox provides runtime dynamic and static analysis reports. Mobile-Sandbox analyzes the android apk for any malicious behaviour. If you wish not to display reports publicly, make sure to check “Delete sample after reporting” option.
Have a look at reports of malicious apps generated by Mobile-Sandbox.
Based on sandbox testing on reports page, it displays weather app is malicious or not. Mobile Sandbox uses MD5 hashing for authenticity of the application submitted.
These online report can be useful for research purpose, to know whether a app uses android permissions to access personal data or does it need access to any hardware sensors, if yes then which hardware sensors are used. Also report displays about type of storage used by application.
Sanddroid
Sanddroid is an automatic application analysis system, we can use it same way we used Anubis and Mobile-Sandbox, just submit the apk file and let Sanddroid generate a report after executing the application in its sandbox environment performing Static, Dynamic and Comprehensive analysis.
We know about static and dynamic analysis, but comprehensive analysis might be new for many of us. It contains scores based on level of risk of application. Showing all risky behaviours of applications. Generated report also contains which advertisement modules are used in application.
These are sample reports generated by Sanddroid, it also generated.
Dexter
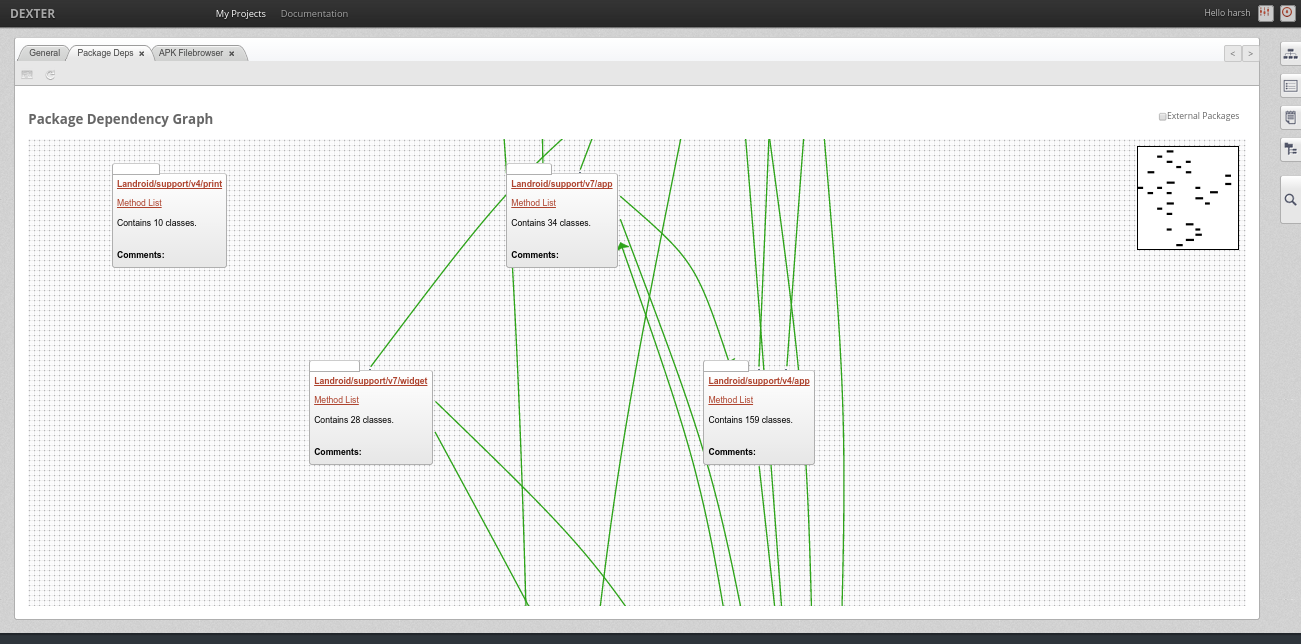
Dexter is another online service used for android static analysis tool, still under public beta phase, as stated on Dexter home page, supports all static analysis data, additionally, showing it in beautiful graphical manner, in form of Package Dependency Graph.
Refer Dexter Docs to know more about Package Dependency Graph.
In Summary
This bring us to the end of this part. In this part, we explored about the usage of some online tools for performing reverse engineering on android apks and doing malware analysis, like Anubis, Mobile-Sandbox,Sanddroid and Dexter.
We shall talk about Reverse Engineering using Virtual Machines in next part. Till than play with all these mentioned tools and perform reverse engineering on some of the malicious APKs and check the malicious reports. See you in next part where we would talk about reverse engineering using virtual machine!